Thu Jan 06 02:11:33 +0000 2022
[tweet] [link]
Out of all the orgs involved in the Maricopa audit, I had assumed CyFir would be the most competent. The report that was just released by the county today blows that assertion into smithereens.
CyFir's conclusions demonstrate anything but competence.
[tweet] [link]
I'm too braindead to go into this in detail at the moment, but I'll give at least 1 example: the "checking for blank passwords" claim.
See the screenshot for the CyFir finding (https://c692f527-da75-4c86-b5d1-8b3d5d4d5b43.filesusr.com/ugd/2f3470_d36cb5eaca56435d84171b4fe7ee6919.pdf).
[tweet] [link]
Luckily for CyFir, the county requested that they redact their screenshots. Had they not done that, their claims would have been debunked within days.
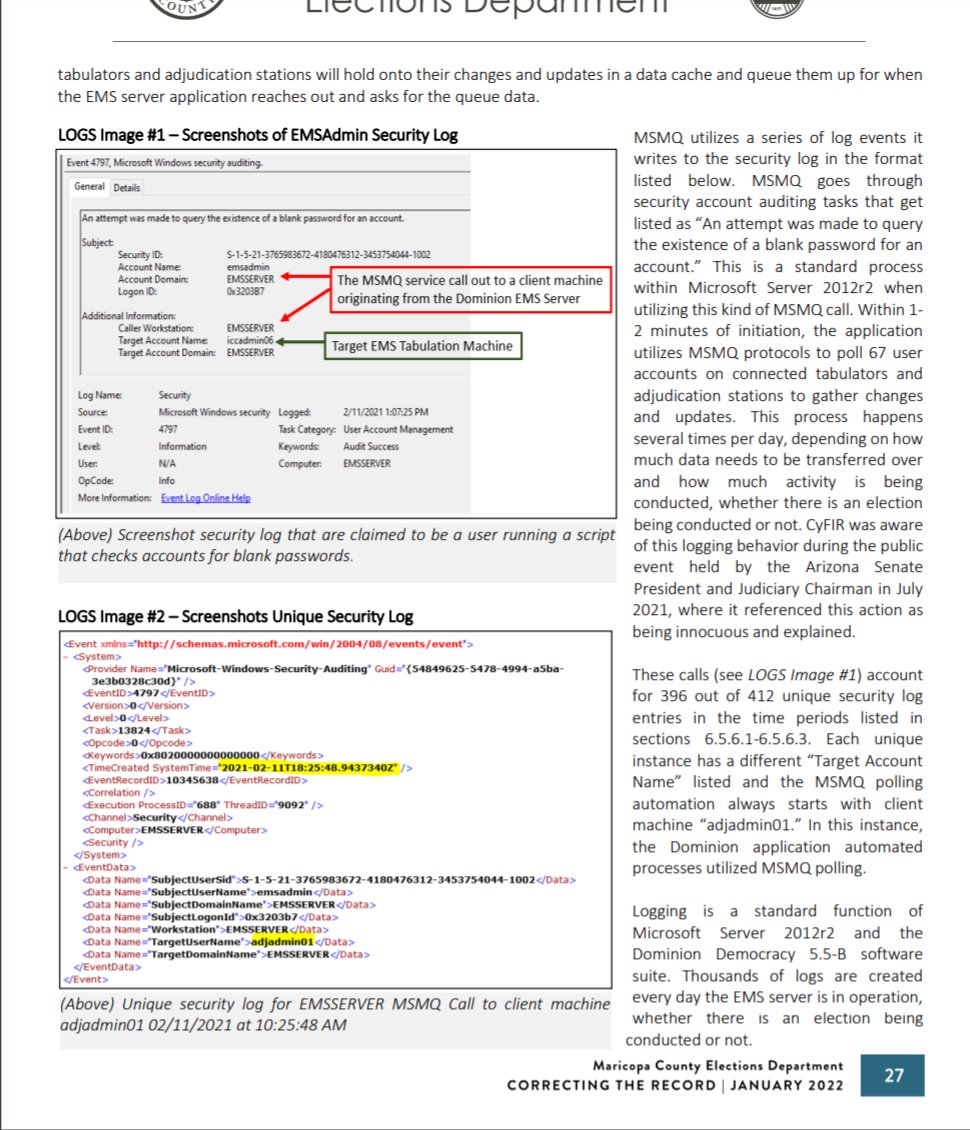
Luckily for us, the county report includes screenshots.
[tweet] [link]
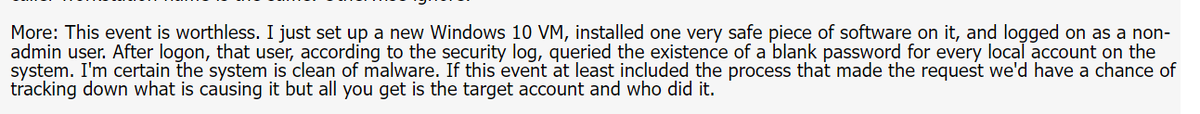
Basically, Windows Event logs are noisy. And event names that sound suspicious typically have a reasonable explanation. This was obviously the case with the "ZOMG BLANK PASSWORD QUERYING HAX0R SCRIPT"
[tweet] [link]
The cause, according to the county, was that the Dominion software utilized the "Microsoft Message Queue" service, which tends to generate these log messages as part of it's normal course of business.
[tweet] [link]
For laypeople, MS event codes and subcodes may as well be hieroglyphics. That's why sites like this exist https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/event.aspx?eventid=4797
And that site very clearly says that the event is not indicative of anything bad